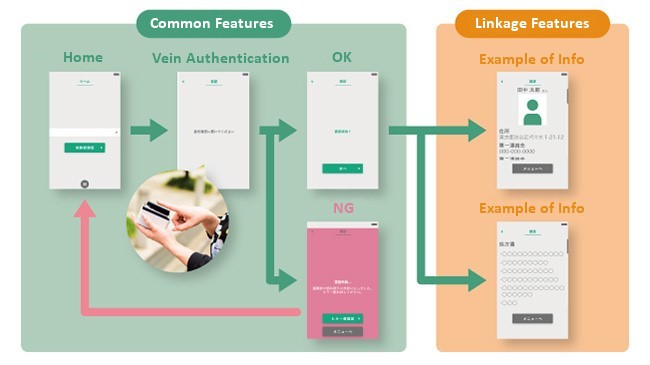
Solution Deployment Utilizing Bluetooth Connected Vein Authentication | Biometrics, Finger Vein Recognition | mofiria

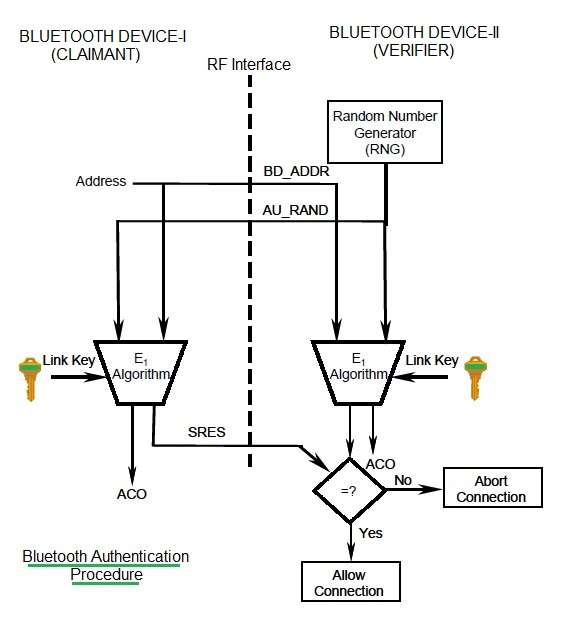
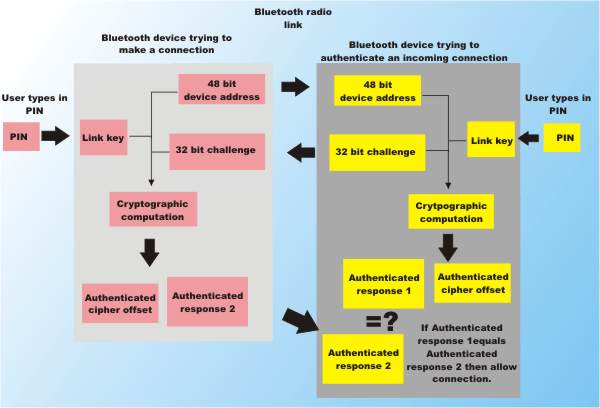
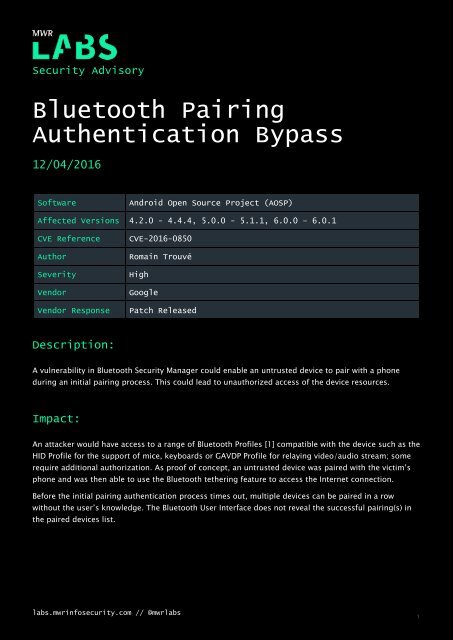
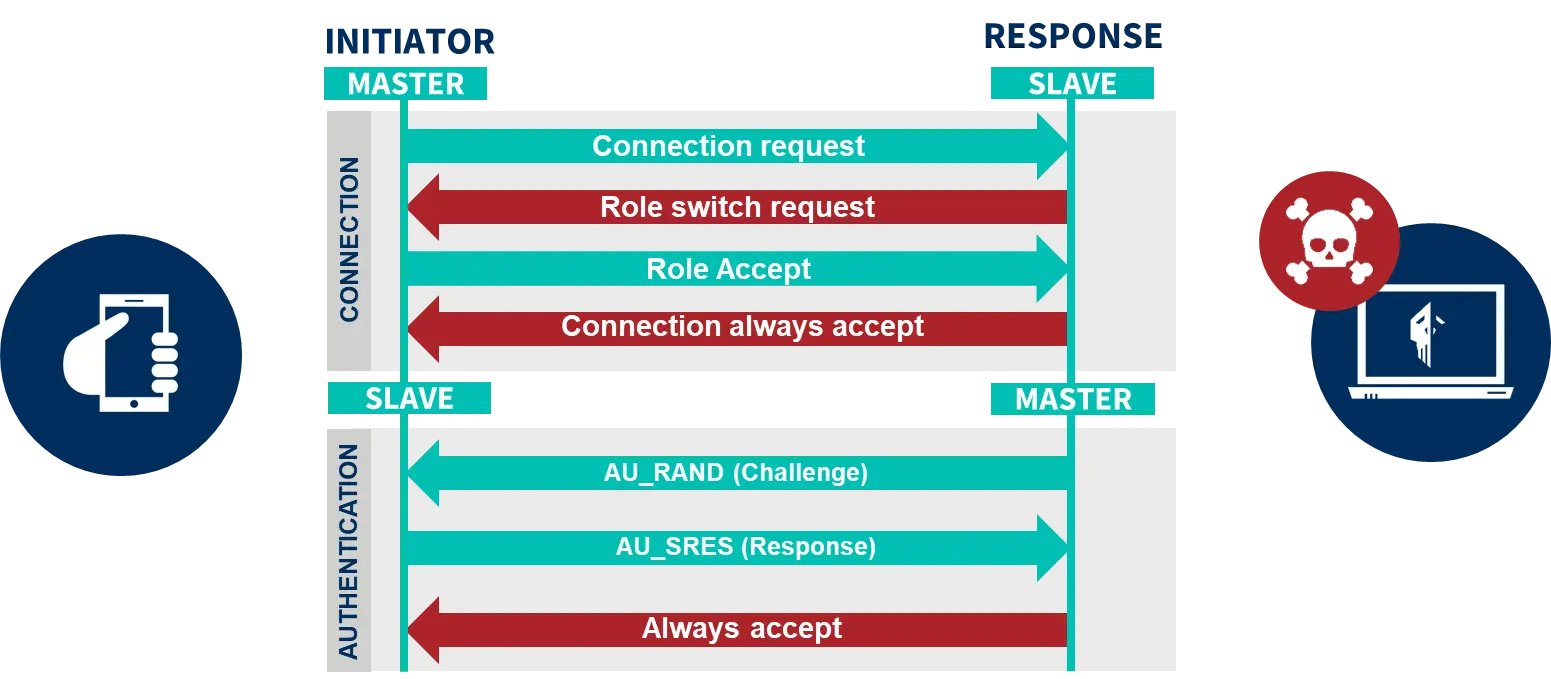
Sensors | Free Full-Text | On Secure Simple Pairing in Bluetooth Standard v5.0-Part I: Authenticated Link Key Security and Its Home Automation and Entertainment Applications

![3: Bluetooth Authentication [159] | Download Scientific Diagram 3: Bluetooth Authentication [159] | Download Scientific Diagram](https://www.researchgate.net/publication/267562281/figure/fig21/AS:669373668814879@1536602527774/Bluetooth-Authentication-159.png)